Never Trust, Always Verify
Zero Trust
RathonTech’s Zero Trust platform blocks internal and external threats by continuously verifying identity and evaluating all access in real time.
Zero Trust with
integrated
and
continuous authentication
-
Zero Trust solution
Enterprise Zero Trust solution integrating SSO - IAM - LDAP - WinLogin - MFA - Anomaly Risk Management (AM). Identity-based continuous validation to block internal and external threats.
-

Never Trust, Always Verify
Zero Trust is a modern security model based on the principle of "Never Trust, Always Verify". By re-verifying trust at every access point—whether it be users, devices, or networks—it overcomes the limitations of traditional perimeter-based security.
-

Authentication-driven security
Our platform combines strong authentication (WinLogin integration, SSO), multi-factor authentication (MFA), centralised directory (LDAP), sophisticated anomaly detection engine (AM) and integrated account/permission management (IAM) to evaluate and grant all access requests in real-time. The key is identity-based continuous validation.
Secure environment with
real-time threat response
-

Continuous user verification
Validate users and devices at every connection, allowing access only when trusted.
-
Principle of least privilege
Minimise security risks by granting only the permissions you need to do your job and immediately revoking unnecessary permissions.
-

Anomaly detection and response
Analyse user login and access patterns to quickly detect anomalies and provide immediate blocking and response.
-

Secure access anywhere
Ensure the same level of security not only on your internal network, but also in the cloud and remote work environments to provide a safe working environment.
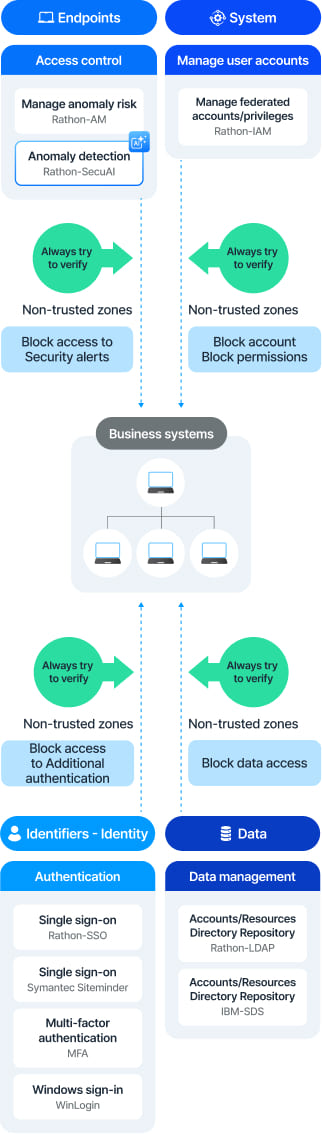
Architecture

-
Resource
IdentificationIdentify all critical resources requiring protection (data, applications, services, etc.). These resources may reside in various locations, including on-premises data centres, cloud environments, and SaaS platforms. -
Transaction
Flow MappingUnderstand how data flows between users, devices, applications, and resources. Map all data movement paths within the organisation, considering access routes from multiple locations such as headquarters, branch offices, remote working environments, public networks, data centres, and VPN connections. -
Policy Design
Establish security policies defining who can access which resources, under what conditions, and from where. These policies are managed by the Policy Administration component and must be sufficiently stringent to enforce the principle of least privilege and continuous validation. -
Monitoring
and LoggingBuild a Policy Engine that evaluates access requests against predefined policies. This engine makes reasoned access decisions using inputs such as data access policies, Public Key Infrastructure (PKI), identity management, SIEM, CDM, industry regulatory compliance requirements, threat intelligence, and activity logs. -
PDP, Policy
Decision PointImplement the Policy Enforcement Point (PEP) that actually executes the decisions made by the Policy Engine. This component sits between the user/device and the resource, ensuring only verified and authorised requests reach the resource. -
PEP, Policy
Enforcement PointContinuously monitor all user and device activity. Update and refine policies based on data gathered from threat intelligence and activity logs, enabling adaptation to new threats and behavioural patterns. -
Secure
CommunicationsAll communications on the data plane must be encrypted, and no implicit trust is granted to any network segment or device. (The blue dotted line "No Implicit Trust" in the image illustrates this) -
Policy Review
and UpdateSecurity policies are continuously reviewed and updated to respond to new threats and the organisation's evolving requirements. Regular audits and regulatory compliance reviews ensure the effective maintenance of the Zero Trust framework.
Seamless authentication and access control with Zero Trust
Zero Trust platform
Solution Map
IAM
Authentication
Cryptographic Module
Zero Trust
Rathon-Platform Services
(Single sign-on, single account/
permission management)